Hfv -hidden Folder Virus- Cleaner Pro «FREE - 2027»
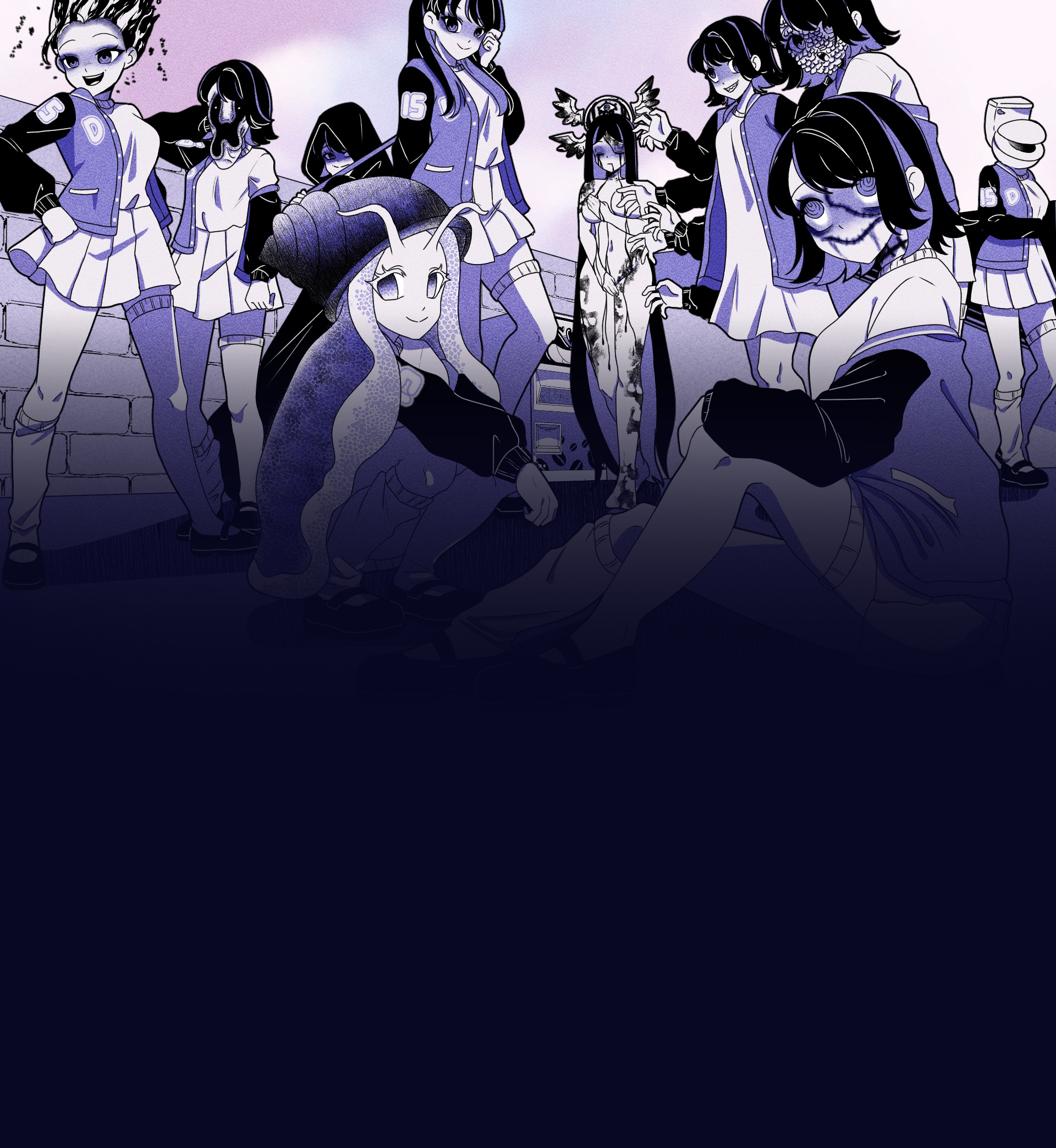
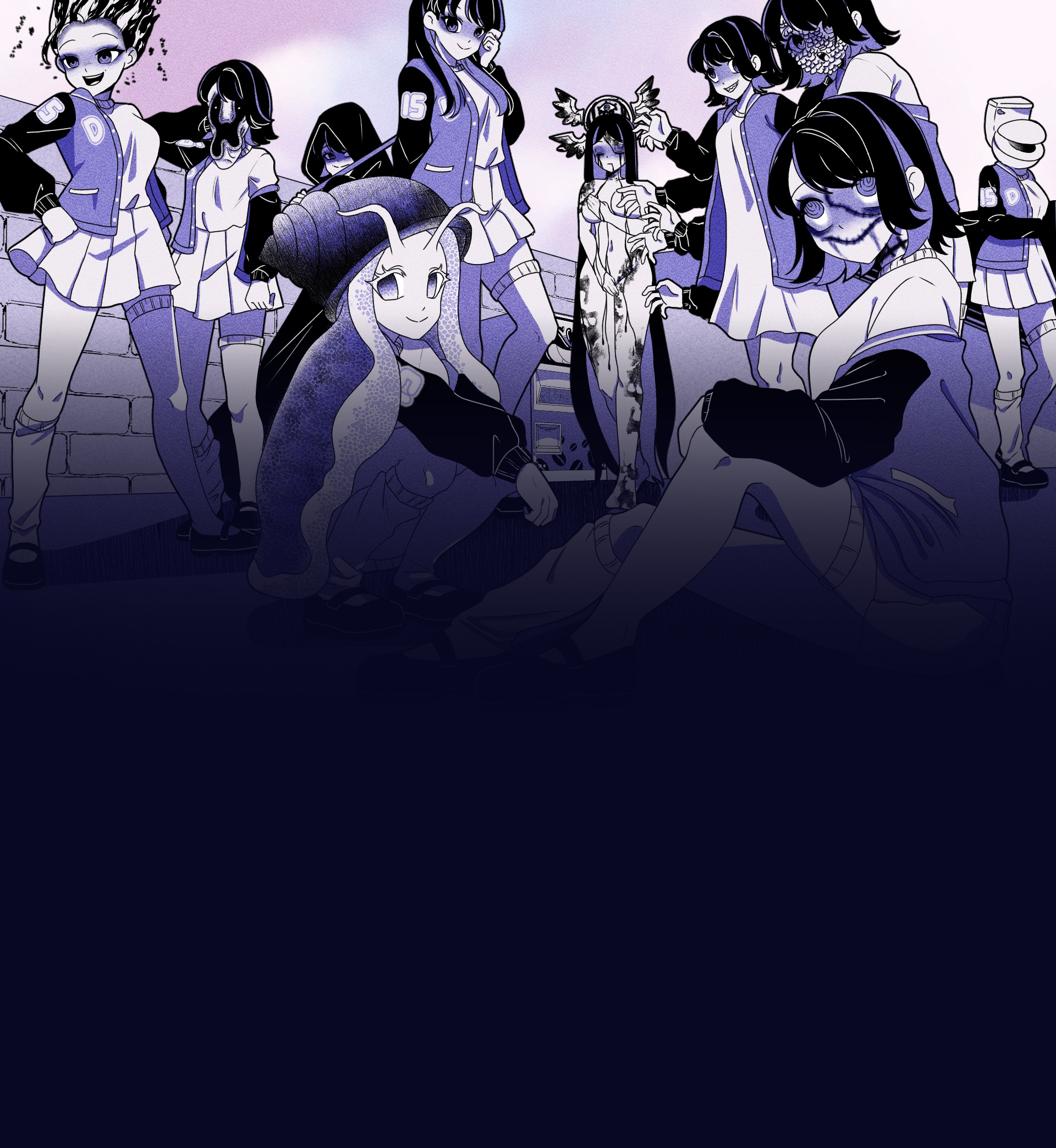
A unique visual novel where you explore a mysterious coffee machine that can dispense any liquid imaginable
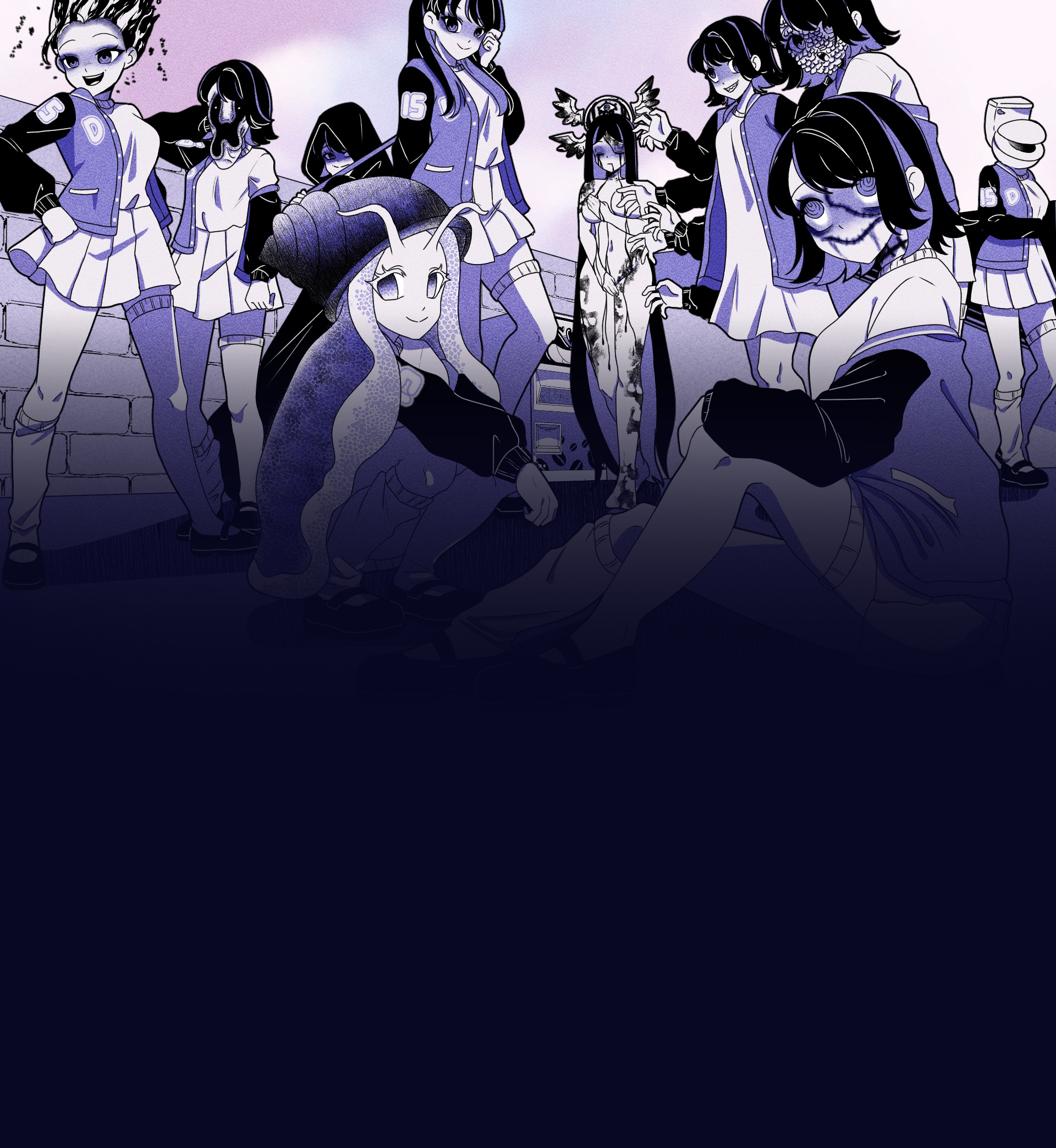
A unique visual novel where you explore a mysterious coffee machine that can dispense any liquid imaginable
Experience this unique visual novel interactive simulation game directly in your browser. No downloads required!
Click the button below to load and start the game
Visual Novel
30-60 minutes
Single Player
Web Browser
However, the legitimacy and efficacy of such “Pro” labeled software immediately raise red flags within the cybersecurity community. The market is saturated with fake antivirus programs and rogue security software that exploit the very fears they claim to soothe. An application named “HFV - Hidden Folder Virus - Cleaner Pro” often operates in a gray area. While a genuine version might successfully clean a USB drive, many variants proliferated through download aggregators are themselves bundled with adware, spyware, or even the original hidden folder virus. In a cruel irony, a user seeking to disinfect their computer may inadvertently pay for or download a program that reinstates the infection or steals credentials. Consequently, the term “Pro” is frequently a marketing gimmick rather than a certification of superior quality, suggesting that the user is better served by established, open-source tools or manual command-line solutions than by obscure proprietary software.
In the landscape of digital security, few nuisances are as persistent and misunderstood as the malware commonly referred to as the "Hidden Folder Virus" (HFV). This affliction, typically affecting removable USB drives and local storage, exploits a fundamental feature of the Windows operating system by hiding user folders and replacing them with executable files of the same name. In response to this threat, a class of software has emerged, notably represented by programs bearing titles such as “HFV - Hidden Folder Virus - Cleaner Pro.” While such applications promise a straightforward solution, a critical examination reveals a complex paradox: these tools serve as both a necessary remedy for an endemic problem and a potential vector for further security risks.
In conclusion, “HFV - Hidden Folder Virus - Cleaner Pro” stands as a representative artifact of the endpoint security market. It addresses a genuine, tangible nuisance that continues to plague educational institutions, printing shops, and home users who frequently exchange USB drives. Yet, its very existence is problematic. While it may, in its most benign form, offer a convenient graphical interface for fixing a common problem, the potential for malicious impersonation and the reinforcement of poor user habits render it a double-edged sword. Ultimately, the most effective “cleaner pro” is not a piece of software, but an informed user who understands the value of viewing hidden system files and verifying executable extensions. In the arms race between virus writers and cleanup utilities, the latter can only ever be a temporary salve—never a permanent shield.
Discover what makes Anomalous Coffee Machine an unforgettable gaming experience
Interact with a mysterious vending machine that can dispense any liquid imaginable, possible or impossible.
Type in any word you can think of and see if the machine can dispense it. Endless possibilities await.
Experience a wide range of transformations and effects based on what you choose to drink.
Enjoy a rich visual experience with numerous animated scenes and visual effects.
Immerse yourself in an extensive narrative with over 100,000 words of dialogue and story content.
Interact with a mysterious girl who guides you through the experience of the anomalous machine.
However, the legitimacy and efficacy of such “Pro” labeled software immediately raise red flags within the cybersecurity community. The market is saturated with fake antivirus programs and rogue security software that exploit the very fears they claim to soothe. An application named “HFV - Hidden Folder Virus - Cleaner Pro” often operates in a gray area. While a genuine version might successfully clean a USB drive, many variants proliferated through download aggregators are themselves bundled with adware, spyware, or even the original hidden folder virus. In a cruel irony, a user seeking to disinfect their computer may inadvertently pay for or download a program that reinstates the infection or steals credentials. Consequently, the term “Pro” is frequently a marketing gimmick rather than a certification of superior quality, suggesting that the user is better served by established, open-source tools or manual command-line solutions than by obscure proprietary software.
In the landscape of digital security, few nuisances are as persistent and misunderstood as the malware commonly referred to as the "Hidden Folder Virus" (HFV). This affliction, typically affecting removable USB drives and local storage, exploits a fundamental feature of the Windows operating system by hiding user folders and replacing them with executable files of the same name. In response to this threat, a class of software has emerged, notably represented by programs bearing titles such as “HFV - Hidden Folder Virus - Cleaner Pro.” While such applications promise a straightforward solution, a critical examination reveals a complex paradox: these tools serve as both a necessary remedy for an endemic problem and a potential vector for further security risks. hfv -hidden folder virus- cleaner pro
In conclusion, “HFV - Hidden Folder Virus - Cleaner Pro” stands as a representative artifact of the endpoint security market. It addresses a genuine, tangible nuisance that continues to plague educational institutions, printing shops, and home users who frequently exchange USB drives. Yet, its very existence is problematic. While it may, in its most benign form, offer a convenient graphical interface for fixing a common problem, the potential for malicious impersonation and the reinforcement of poor user habits render it a double-edged sword. Ultimately, the most effective “cleaner pro” is not a piece of software, but an informed user who understands the value of viewing hidden system files and verifying executable extensions. In the arms race between virus writers and cleanup utilities, the latter can only ever be a temporary salve—never a permanent shield. However, the legitimacy and efficacy of such “Pro”